Amazon.com: Canon PIXMA TR4720 All-in-One Multifunction Wireless Color Inkjet Printer, Black - Print Copy Scan Fax - 4800 x 1200 dpi, 8.5 x 14, 2-Line LCD Display, Auto Duplex Printing, 20-Sheet ADF : Office Products

PANTUM M7108DW Stampante laser Multifunzione Monocromatica, Copia,Stampa,Scansione, Stampa senza fili, Duplex automatico, Adatto per l'ufficio e l'uso Domestico : Amazon.it: Informatica

PANTUM M7108DW Multifunzione Stampante Laser Copia/Stampa/Scansione Bianco/Nero Wireless con Stampa fronte/retro Automatica : Amazon.it: Informatica

Amazon.com: Canon TS9521C All-In-One Wireless Crafting Photo Printer, 12X12 Printing, White, Amazon Dash Replenishment Ready : Office Products

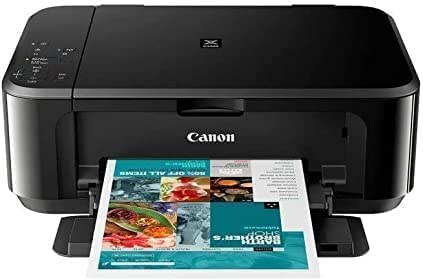
Canon Pixma MP280 Stampante multifunzione a colori | seguiprezzo/segui Amazon , grafici cronologia prezzo Amazon, monitoraggi prezzo Amazon, avvisi diminuzione prezzo Amazon | camelcamelcamel.com

Canon i-SENSYS MF3010 Stampante Laser Multifunzione Monocromatica, colore: Nero : Amazon.it: Informatica

Amazon.com: Canon TS9521C All-In-One Wireless Crafting Photo Printer, 12X12 Printing, White, Amazon Dash Replenishment Ready : Office Products