Halloween Rock Disco Kvindelig sanger Kostumer Kvinder Vintage 70'erne 80' erne Hippie Cosplay Kostume Scene Performance Dansetøj | Fruugo DK

1980'erne Kostume 70'erne, 80'erne' Neon Disco Dans Fest Kostume Tilbehør Handsker Ben-temperaturvisning Smykker Mode Tilbehør Tjene / Engros ~ Smorrebrodgrill.dk

På tilbud! Voksne kvinder hippie kostume i 60'erne, 70'erne woodstock hippie diskotek retro musik fantasi fancy kjole part halloween kostume < Kvindernes dragt \ Trekloeveret.dk

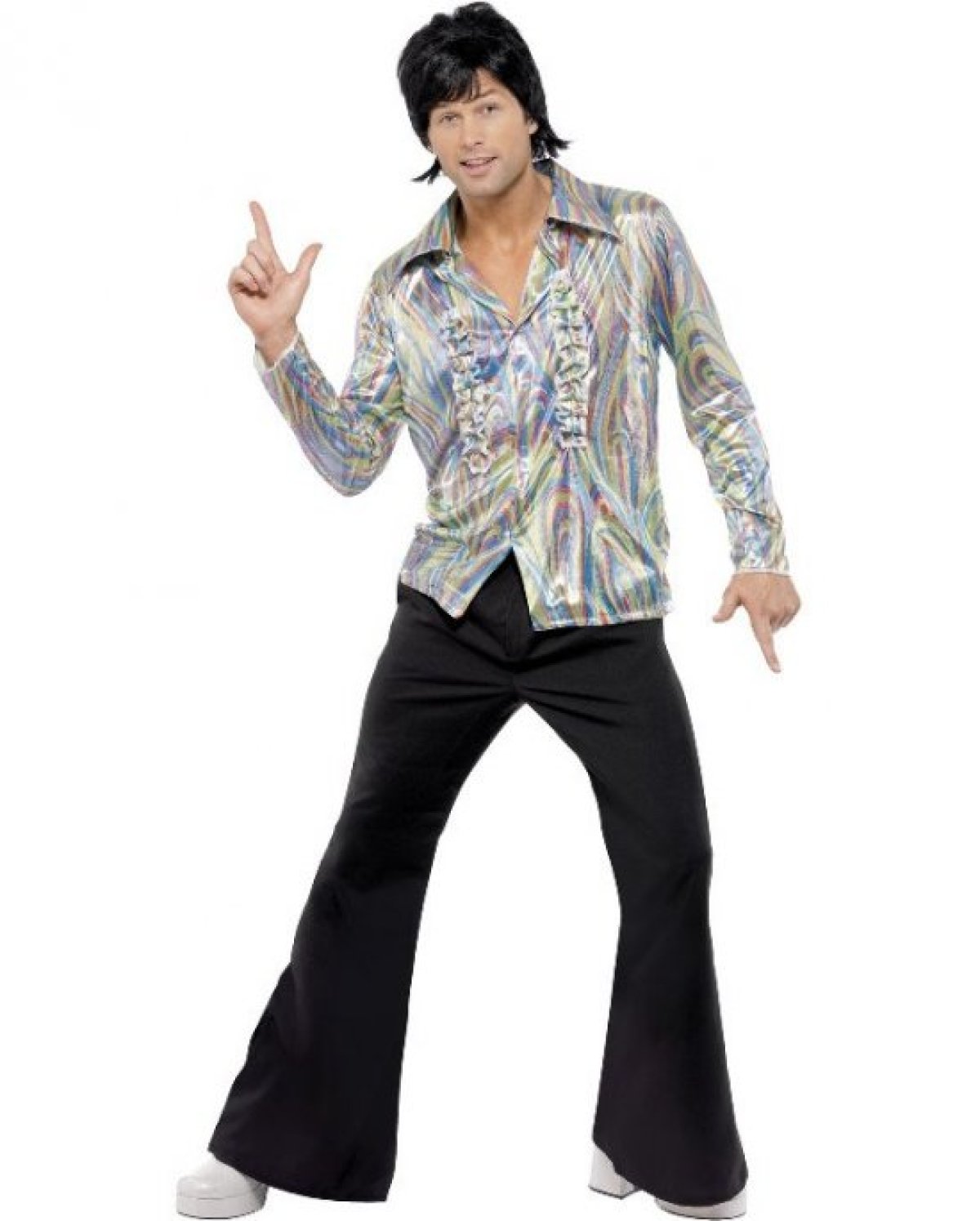
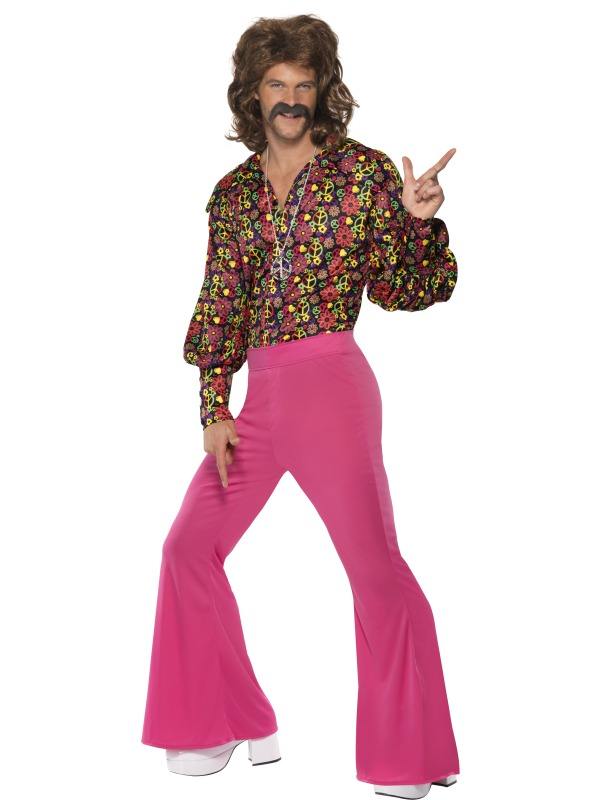
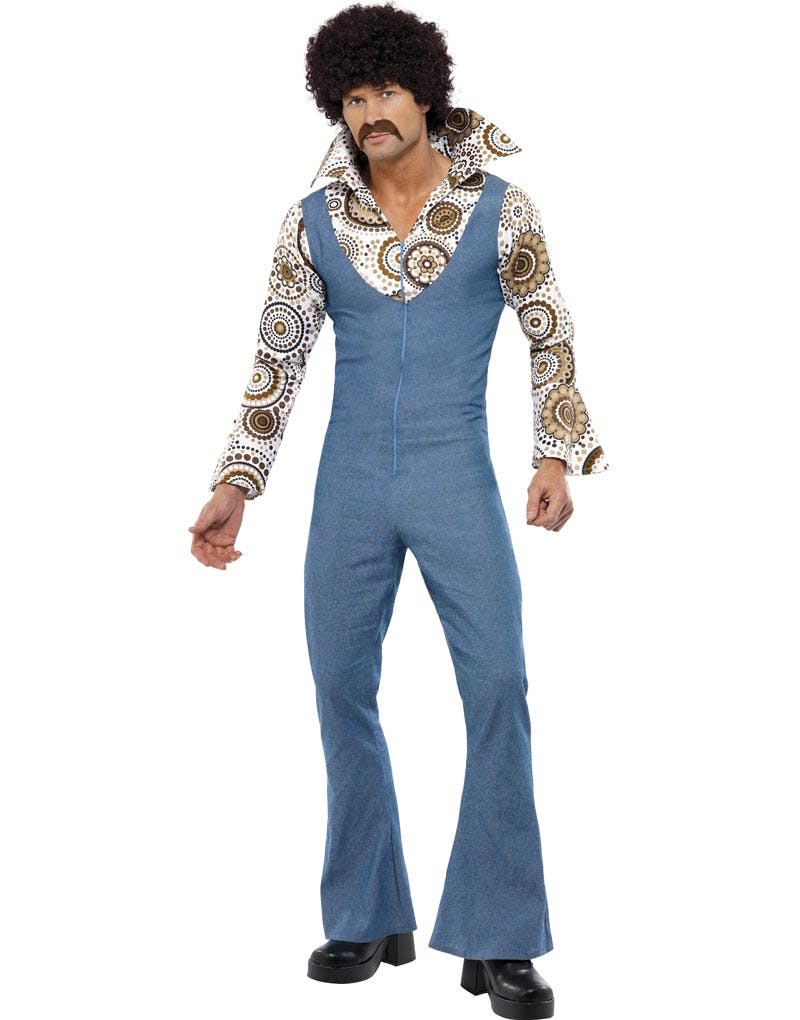
22 idéer på 70'er disco - musical - kostumer og rekvisitter | kostumer, trompetbukser, linda ronstadt